You are looking to hire a vendor. You need to know how trustworthy they are when it comes to cybersecurity. You must follow the industry standards and look at their SOC audits. But which one should you request and analyze? Read through our short explanation of each of these and find out.
Vendor SOC 1, 2 and 3 – How Are They Different?
Auditing companies prepare the SOC report for companies that handle sensitive financial data or are responsible for data security. There are three types of SOC reports created by external auditors based on a framework set by the American Institute of Certified Public Accountants (AICPA). So if a vendor has a good SOC report, it means they are following best practices. But SOC 1, SOC 2 and SOC 3 are generated for different purposes and for different audiences. So understanding the differences is important for getting the best use out of them.
Background Of Vendor SOC Reports
If a vendor wants to appear trustworthy to its potential clients then they will prepare for a SOC audit. To examine if the use of security plans and technologies on a day-to-day basis it is done through a long term audit (Type 2). But vendors use a one-time audit (Type 1) for demonstrating their awareness of security risks and potential ways to deal with them. Here, their security framework is audited and not its day-to-day execution.
Significance Of A Vendor’s SOC 1
This detailed report on the vendor’s internal controls relates to how they process and secure a customer’s financial information. It is used by the customer’s management and external auditors. If the vendor is going to manage your billing, payroll management software, financial reporting software, etc then this is the report you should be looking at.
Significance Of A Vendor’s SOC 2
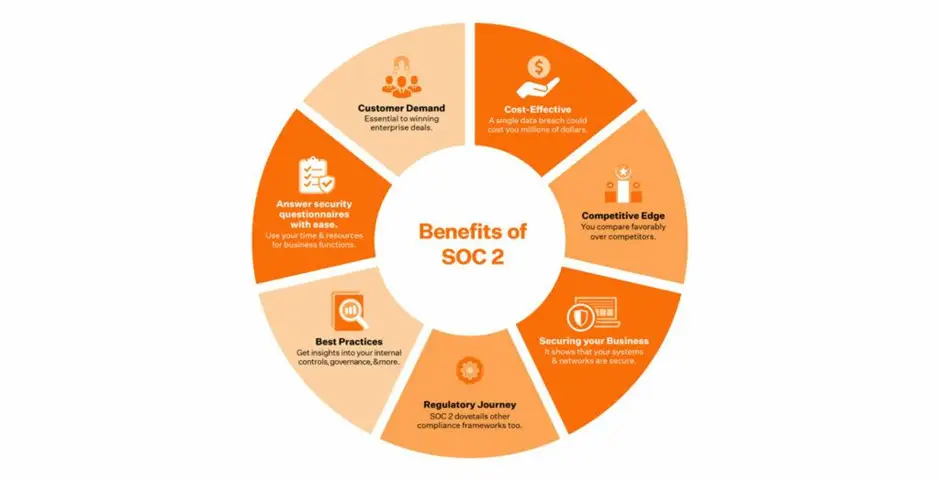
This is a detailed report on the vendor’s internal controls relevant to five Trust Service Criteria – security, availability, processing integrity, confidentiality, and privacy. Out of these, security is a compulsory criteria for your vendor to clear the SOC 2. The other criteria are optional. Based on the customer’s requirement the vendor can provide the SOC 2 for any combination of these criteria. It is mainly used by customers and their prospective clients. If the vendor is going to provide Cloud services, HR management services, SaaS, etc then this report is what you should be concerned with.
Significance Of A Vendor’s SOC 3
It is a short report covering the same areas as the SOC 2 and applicable for data security maintained by the vendor. It only uses long term audits (Type 2). It is similar to the SOC 2 report with an abbreviated opinion of the auditor for general use. System descriptions are brief to protect sensitive information. Lists of internal control and tests of operational efficiency are completely excluded. So this report is only useful in the initial stages to establish that the vendor does have a SOC 2 report.
Some Tips For Reviewing Vendor SOC Reports
Here are some tips for reviewing your vendor’s SOC reports that will help you get the most value out of them.
- First thing to ask is whether the product you use is included within the scope of the SOC report. Large vendors have multiple reports and all the SOC reports do not include in all the products.
- Next you should ask what the audit period of the most recent audit was. If it was the report issued less than one year ago then it may not reflect a continuous practice.
- Then ask if the vendor has a SOC audit performed every year. Some vendors may skip a few years as these audits are expensive but doing them each year reflects consistency.
- Check if the vendors have year-round audit periods. If not then find out why.
- Finally see if your vendor has critical vendors of their own that impact you directly. If they do then do not proceed without the SOC of the sub-vendors.
Requesting and Analyzing Vendor SOC Reports
Requesting and Analyzing vendor reports is essential to establish the controls they have in place relevant to financial and data security. It can help you decide if a vendor is right for you. It can also help you specify if they need to update or improve any part of their controls pertaining to any product you wish to use. This can be a long and drawn out process.




