Download this free Functional Requirement Specification Document template and use it for your new project. Scroll down to the bottom of the page for the download link.
1 Introduction
<Provide an overview of the system and some additional information to place the system in context>
1.1 Purpose
<Provide an overall description of the Functional Requirement Specifications, its purpose. Reference the system name and identifying information about the system to be implemented>
1.2 Scope
<Discuss the scope of the document and how its accomplishes its purpose>
1.3 Background
<Describe the organization and its overall responsibilities. Describe who is producing the document and why>
1.4 References
<List references and controlling documents, including: meeting summaries, white papers, other deliverables, etc.>
1.5 Acronyms and Abbreviations
<This subsection provide the definitions of all terms, acronyms and abbreviations required to properly interpret the Functional Requirement Specifications document>
For example:
FRS Functional Requirement Specification
1.6 Assumptions and Constraints
<Provide a list of contractual or task level assumptions and/or constraints that are preconditions to preparation of the FRS. Assumptions are future situations beyond the control of the project, whose outcomes influence the success of a project>
1.6.1 Assumptions
<Example of assumptions include: availability of a technical platform, legal changes and policy decisions>
1.6.2 Constraints
<Constraints are boundary conditions on how the system must be designed and constructed. Example include: legal requirements, technical standards, strategic decisions.
- Constraints exist because of real business conditions. For example, a delivery date is a constraint only if there are real business consequences that will happen as a result of not meeting the date. If failing to have the subject application operational by the specified date places the organization in legal default, the date is a constraint.
- Preferences are arbitrary. For example, a date chosen arbitrarily is a preference. Preferences, if included in the FRS, should be noted as such>
1.7 Document Overview
<Provide a description of the document organization>
2 Methodology
<Describe the overall approach used in the determination of the FRS contents. Describe the modeling method(s) so non-technical readers can understand what they are conveying>
3 Functional Requirements
3.1 Context
<Provide a context diagram of the system, with explanations as applicable. The context of a system refers to the connections and relationships between the system and its environment>
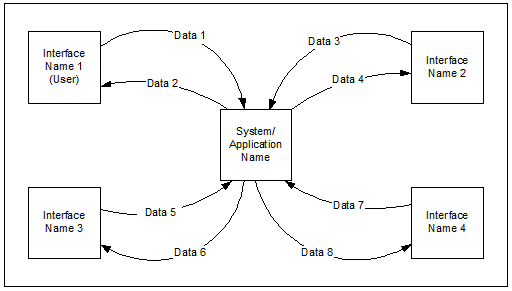
Figure 1 : Generic Context Diagram
3.2 User Requirements
<Provide requirements of the system, user or business, taking into account all major classes/categories of users. Provide the type of security or other distinguishing characteristics of each set of users. List the functional requirements that compose each user requirement. As the functional requirements are decomposed, the highest level functional requirements are traced to the user requirements. Inclusion of lower level functional requirements is not mandatory in the traceability to user requirements if the parent requirements are already traced to them.
User requirement information can be in text or process flow format for each major user class that shows what inputs will initiate the system functions, system interactions, and what outputs are expected to be generated by the system. The scenarios should be comprehensive, to the extent that all user types and all major functions are covered. Give each user requirement a unique number. Typically, user requirements have a numbering system that is separate from the functional requirements >
3.3 Data Flow Diagrams
<Decompose the context level diagrams to determine the functional requirements. Data flow diagrams should be decomposed down to the functional primitive level. These diagrams are further decomposed during design>
3.4 Logical Data Model/Data Dictionary
[Create the initial Logical Data Model. Describe data requirements by providing data entities, decomposition, and definitions in a data dictionary. The data requirements describe the business data needed by the application system. Data requirements do not describe the physical database and are not at the level of identifying field names.]
3.5 Functional Requirements
<List the functional requirements of the system>
3.5.1 Functional Requirements Group 1
<List the functional requirements for each functional requirement group>
| Section/Requirement ID | Requirement Definition |
| FR1.0 | The system shall <parent requirement group 1> |
| FR1.1 | The system shall <child/parent requirement > |
| FR1.1.1 | The system shall <child requirement > |
| FR1.1.2 | The system shall <child requirement> |
Table 1 : Sample Requirements Group 1
3.5.2 Functional Requirements Group 2, etc.
<List the functional requirements of the system>
4 Other Requirements
<Describe the non-behavioral requirements>
4.1 Interface Requirements
<Describe the user interfaces that are to be implemented by the system>
4.1.1 Hardware Interfaces
<Define hardware interfaces supported by the system, including logical structure, physical addresses, and expected behavior>
4.1.2 Software Interfaces
<Name the applications with which the subject application must interface. State the following for each such application: name of application, external owner of application, interface details (only if determined by the other application).
It is acceptable to reference an interface control document for details of the interface interactions>
4.1.3 Communications Interfaces
<Describe communications interfaces to other systems or devices, such as local area networks>
4.2 Data Conversion Requirements
<Describe the requirements needed for conversion of legacy data into the system>
4.3 Hardware/Software Requirements
<Provide the description of the hardware and software platforms needed to support the system>
4.4 Operational Requirements
<Provide the operational requirements in this section.
Do not state how these requirements will be satisfied. For example, in the Reliability section, answer the question, “How reliable must the system be”? Do not state what steps will be taken to provide reliability.
Distinguish preferences from requirements. Requirements are based on business needs, preferences are not. If, for example, the user requires a special response but does not have a business-related reason for it, that requirement is a preference.
Other applicable requirements on system attributes may be added to the list of subsections below.
Operational requirements describe how the system will run and communicate with operations personnel>
4.4.1 Security and Privacy
<Provide a list of the security requirements using the following criteria:
A. State the consequences of the following breaches of security in the subject application:
- Loss or corruption of data
- Disclosure of secrets or sensitive information
- Disclosure of privileged/privacy information about individuals
- Corruption of software or introduction of malware, such as viruses
- State the type(s) of security required. Include the need for the following as appropriate:
- Physical security.
- Access by user role or types.
- State access control requirements by data attribute. For example, one group of users has permission to view an attribute but not update it while another group of users has permissions to update or view it.
- State access requirements based on system function. For example, if there is a need to grant access to certain system functions to one group of users, but not to another. For example, “The system shall make Function X available to the System Administrator only”.
- State if there is a need for certification and accreditation of the security measures adopted for this application.
The Security Section describes the need to control access to the data. This includes controlling who may view and alter application data.>
4.4.2 Audit Trail
<List the activities recorded in the application’s audit trail. For each activity, list the data recorded>
4.4.3 Reliability
<A. State the following in this section:
- State the damage can result from failure of this system—indicate the criticality of the software, such as:
- Loss of human life
- Complete or partial loss of the ability to perform a mission-critical function
- Loss of revenue
- Loss of employee productivity
- What is the minimum acceptable level of reliability?
B. State required reliability:
- Mean-Time-Between-Failure is the number of time units the system is operable before the first failure occurs.
- Mean-Time-To-Failure is the number of time units before the system is operable divided by the number of failures during the time period.
- Mean-Time-To-Repair is the number of time units required to perform system repair divided by the number of repairs during the time period.
Reliability is the probability that the system processes work correctly and completely without being aborted.>
4.4.4 Recoverability
<Answer the following questions in this section:
A. In the event the application is unavailable to users (down) because of a system failure, how soon after the failure is detected must function be restored?
B. In the event the database is corrupted, to what level of currency must it be restored? For example “The database must be capable of being restored to its condition of no more than 1 hour before the corruption occurred”.
C. If the processing site (hardware, data, and onsite backup) is destroyed, how soon must the application be able to be restored?
Recoverability is the ability to restore function and data in the event of a failure.>
4.4.5 System Availability
<State the period during which the application must be available to users. For example, “The application must be available to users Monday through Friday between the hours of 6:30 a.m. and 5:30 p.m. EST. If the application must be available to users in more than one time zone, state the earliest start time and the latest stop time. Consider daylight savings time, too.
Include use peak times. These are times when system unavailability is least acceptable.
System availability is the time when the application must be available for use. Required system availability is used in determining when maintenance may be performed.>
4.4.6 General Performance
<Describe the requirements for the following:
A. Response time for queries and updates
B. Throughput
C. Expected rate of user activity (for example, number of transactions per hour, day, or month, or cyclical periods)
Specific performance requirements, related to a specific functional requirement, should be listed with that functional requirement.>
4.4.7 Capacity
<List the required capacities and expected volumes of data in business terms. Do not state capacities in terms of system memory requirements or disk space—if growth trends or projections are available, provide them>
4.4.8 Data Retention
<Describe the length of time various forms of data must be retained and the requirements for its destruction.
For example, “The system shall retain application information for 3 years”. Different forms of data include: system documentation, audit records, database records, and access records>
4.4.9 Error Handling
<Describe system error handling>
4.4.10 Validation Rules
<Describe system validation rules>
4.4.11 Conventions/Standards
<Describe system conventions and standards followed.
For example: Microsoft standards are followed for windows, Institute of Electrical and Electronics Engineers (IEEE) for data formats, etc.>
Click here to download Functional Requirement Specification Document template.